AI Products
Customer-facing
Employee-facing
Who We Help
Employee-facing
Platform
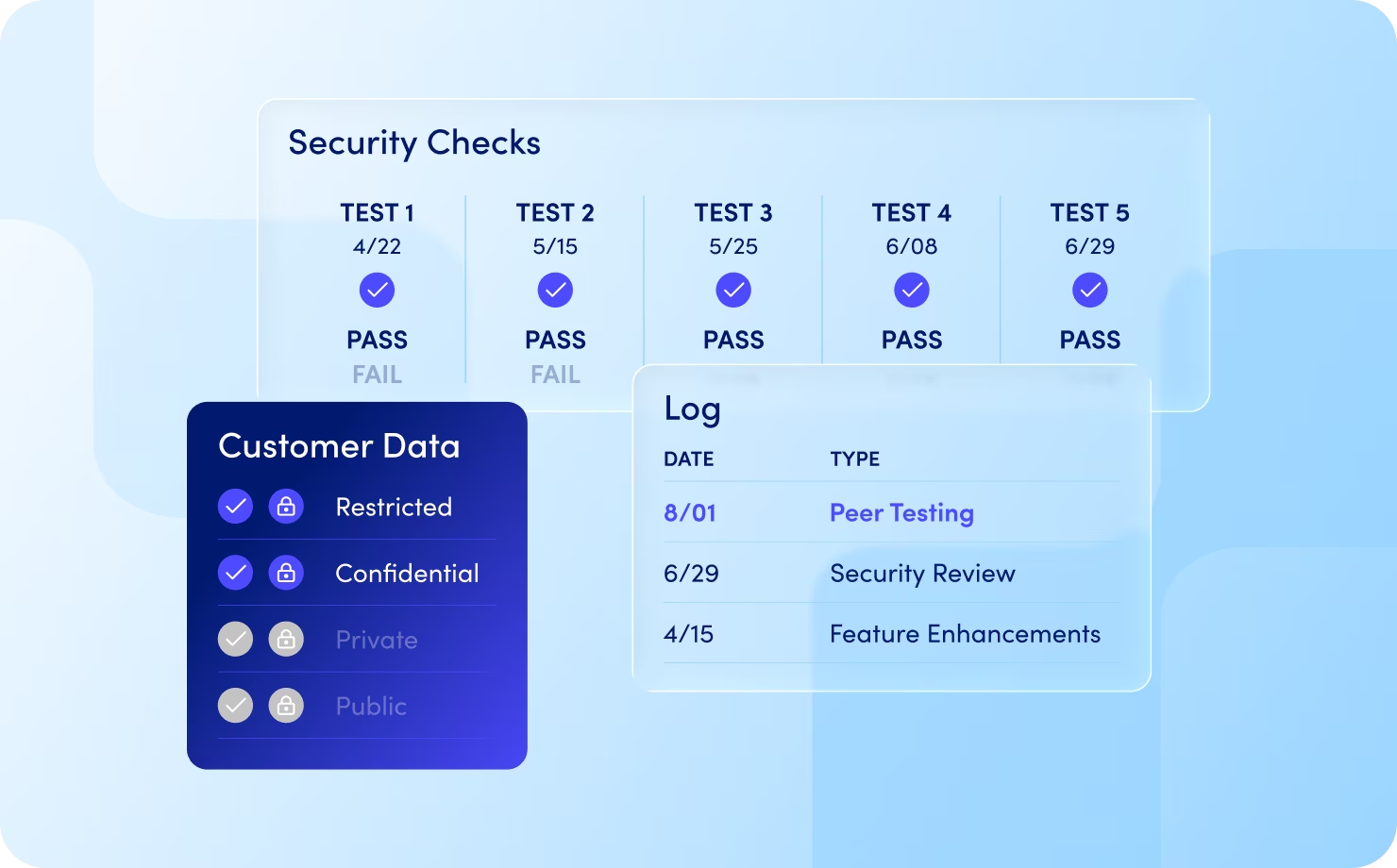
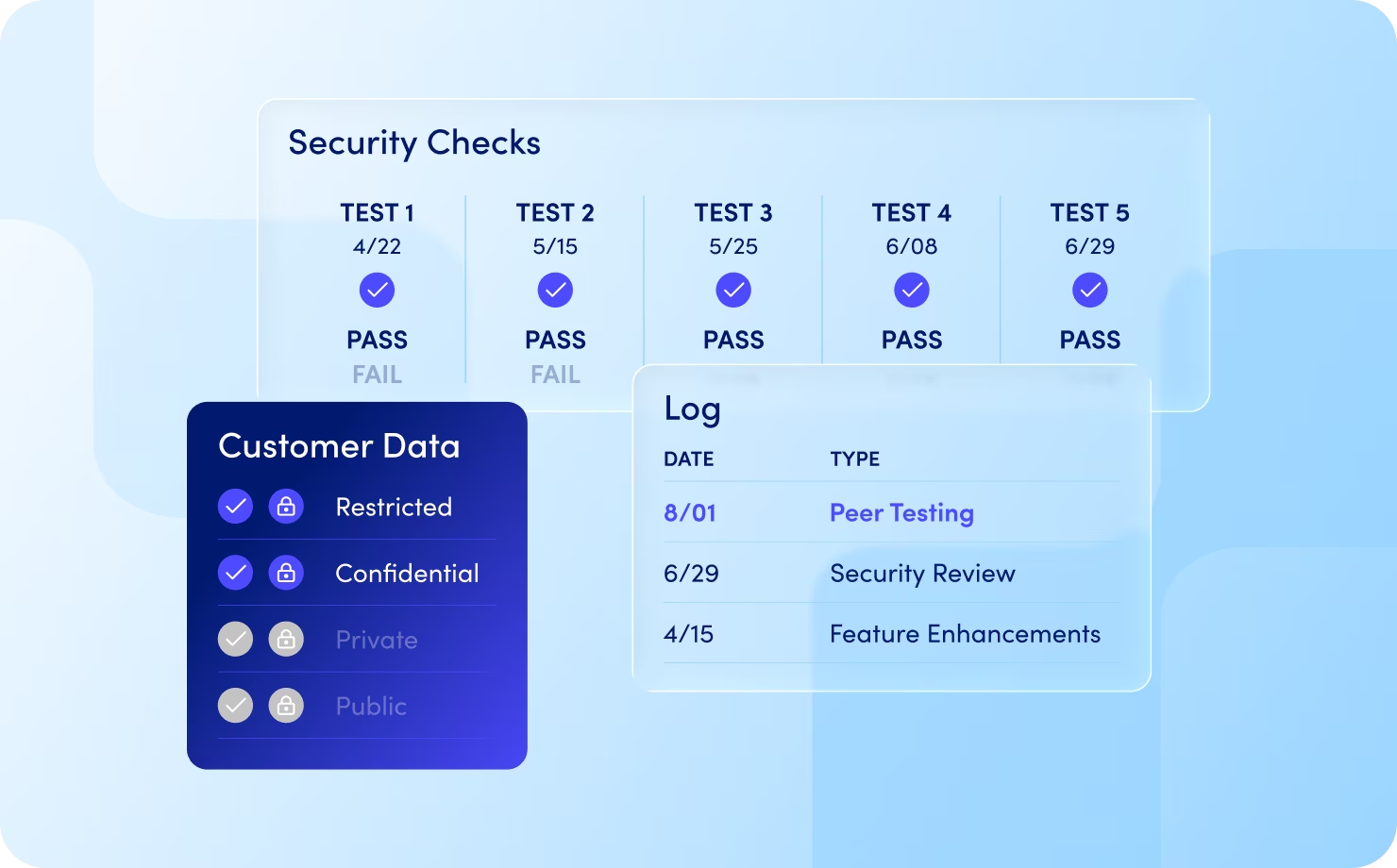
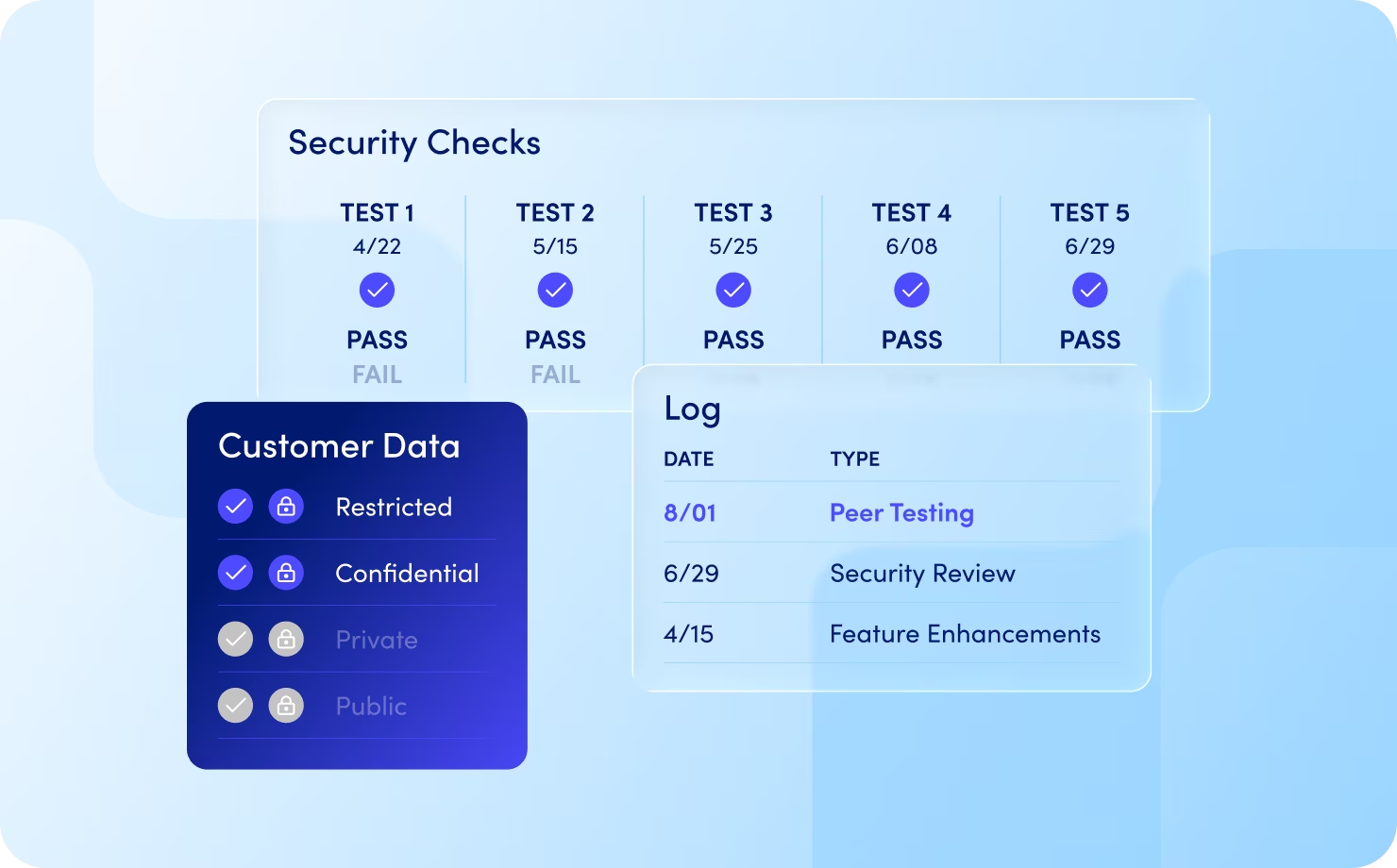
Trust & Security
Copyright ©0000 Posh AI. All Rights Reserved.
Posh’s security, privacy and compliance philosophy is based on a robust, resilient, and proactive approach. We are fully committed to delivering excellence for our 125+ financial institution clients.
Our teams are focused on keeping Posh systems and our client data secure, compliant, and available through a number of security-by-design controls, processes, and procedures.


At Posh, we build our security philosophy on the CIA triad. Here are some examples of how we enforce these principles:



We have processes in place to ensure when our customers leverage the Posh platform and collect some form of PII data, our Data Loss Prevention (DLP) systems performs activities to ensure this information is not persisted.
As part of our privacy-by-design approach, we currently do not persist sensitive PII and make every effort to use alternate identifiers which do not directly identify a data subject. Our Data Protection Impact Assessment (DPIA) procedure ensures we adhere to data minimization controls where possible.

At Posh, we build our security philosophy on the CIA triad. Here are some examples of how we enforce these principles: